The check-in is much more than a formal hurdle – it is the calling card of your event. This is where operational necessity meets the first personal contact, making this moment a strategic anchor point for security, data and guest experience.
A smooth process transforms the entrance from a bottleneck into a valuable service moment. At the same time, mere registrations become verified data points for your reporting. In this way, the check-in forms the foundation for a professional participant journey.
The following four pillars show how colada utilizes this potential for a wide variety of requirements and event formats:
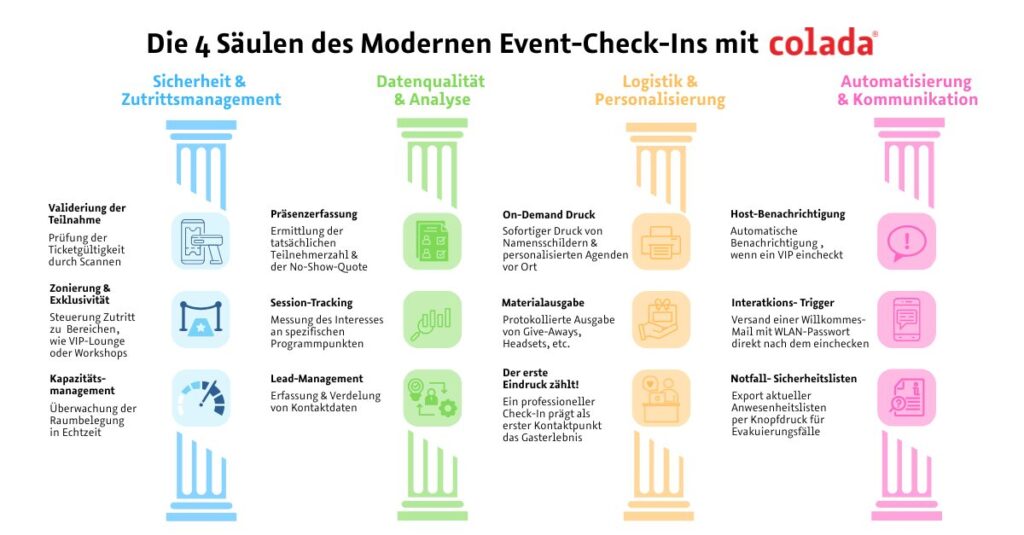
1. security & access management (access control)
This is about controlling and managing the flow of people.
- Validation: Checking eligibility to participate (ticket scan).
- Zoning: Control access to exclusive areas (VIP lounges, backstage, workshop rooms).
- Capacity management: monitoring room occupancy (important for fire safety requirements).
2. data quality & analytics (data insights)
The check-in is the moment when a “registration” becomes a “participant”.
- Attendance recording: Who actually attended? (no-show rate).
- Session tracking: Measurement of interest in specific program items or rooms.
- Lead management: Recording of contact data at trade fair stands or by exhibitors (refinement of data).
- Legal certainty: documentation of attendance (e.g. for certified training or compliance).
3. on-site logistics & personalization (experience)
Everything that guests can get their hands on directly or that makes their stay easier.
- On-demand print: Immediate printing of name badges, table tickets or personalized agendas (prevents waste due to pre-printing).
- Seating information: LIVE information about your table/seat directly at check-in.
- Material distribution: Logged distribution of give-aways, headsets for simultaneous translation or voting equipment.
- Welcome effect: A professional check-in is the first physical touchpoint and shapes the first impression.
4. automation & communication (engagement)
Trigger-based actions that are triggered by the check-in.
- Host notification: Automated SMS/email to account managers when a VIP or important key account checks in.
- Interaction trigger: Sending a welcome email with Wi-Fi password or link to the event app at the exact moment the guest enters the building.
- Safety lists: Export of current attendance lists at the touch of a button for emergencies (evacuation).
Conclusion: check-in good, all good!
The check-in combines central functions such as access control, data collection and communication in a single process. When used correctly, it becomes an effective lever for smooth processes and targeted interactions during the event.